"Will our data be used to train models?"
No. Customer data is contractually excluded from any training, fine-tuning, or model improvement — by us and by every model provider we use. Written into the DPA, not a marketing page.
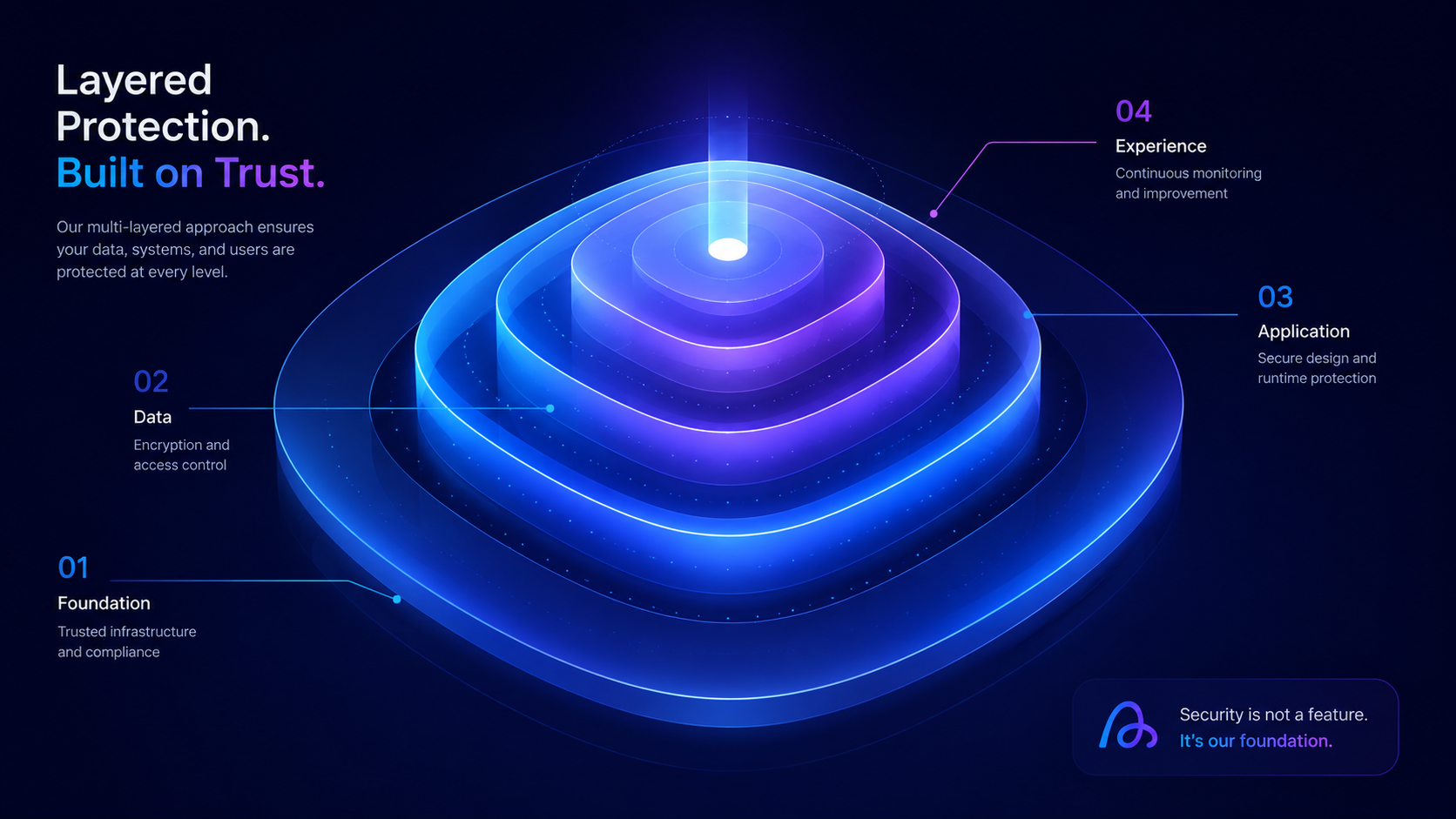
Built for the security, privacy, and compliance demands of regulated, sensitive, and serious businesses. Not bolted on — engineered into every layer, from how we handle your data to how our AI decides what it can see.
Most AI vendors list certifications and call it security. We start with the five questions every C-level asks before they sign — and answer each one in plain language.
No. Customer data is contractually excluded from any training, fine-tuning, or model improvement — by us and by every model provider we use. Written into the DPA, not a marketing page.
Shadow AI is a governance problem, not a tool problem. We help you stand up a sanctioned AI surface so the safer option is also the easier one — with policy, audit, and visibility built in.
Every output traces back to its source. Every high-stakes action requires human approval. Every interaction is logged. We share the burden of getting it right — and the evidence when you're asked to defend a decision.
Your data, prompts, embeddings, and configurations are exportable in standard formats. No proprietary lock-in, no hostage data. We earn renewal by being useful — not by being the only exit.
Customer data can be processed in Singapore or Thailand-resident infrastructure. Cross-border data flows documented. PDPA-aligned DPA in Thai and English. Sub-processor list public.
Your security team shouldn't have to chase us for our DPA, sub-processor list, or DPIA inputs. We publish what we have today and update as we earn more.
Our AI never sees documents the user isn't authorized to see. Access control happens at retrieval — not as a "please don't mention X" instruction to the model.
Singapore, Bangkok, or your own VPC. You decide where compute runs and where data lives. We don't make that an "enterprise add-on."
Sub-processor list, incident history, and audit access — all public or available on request. Trust is earned by showing the work, not promising it.
Every conversation, every document, every action moves through seven independently-secured layers — each owned by a different part of our system, each independently audited.
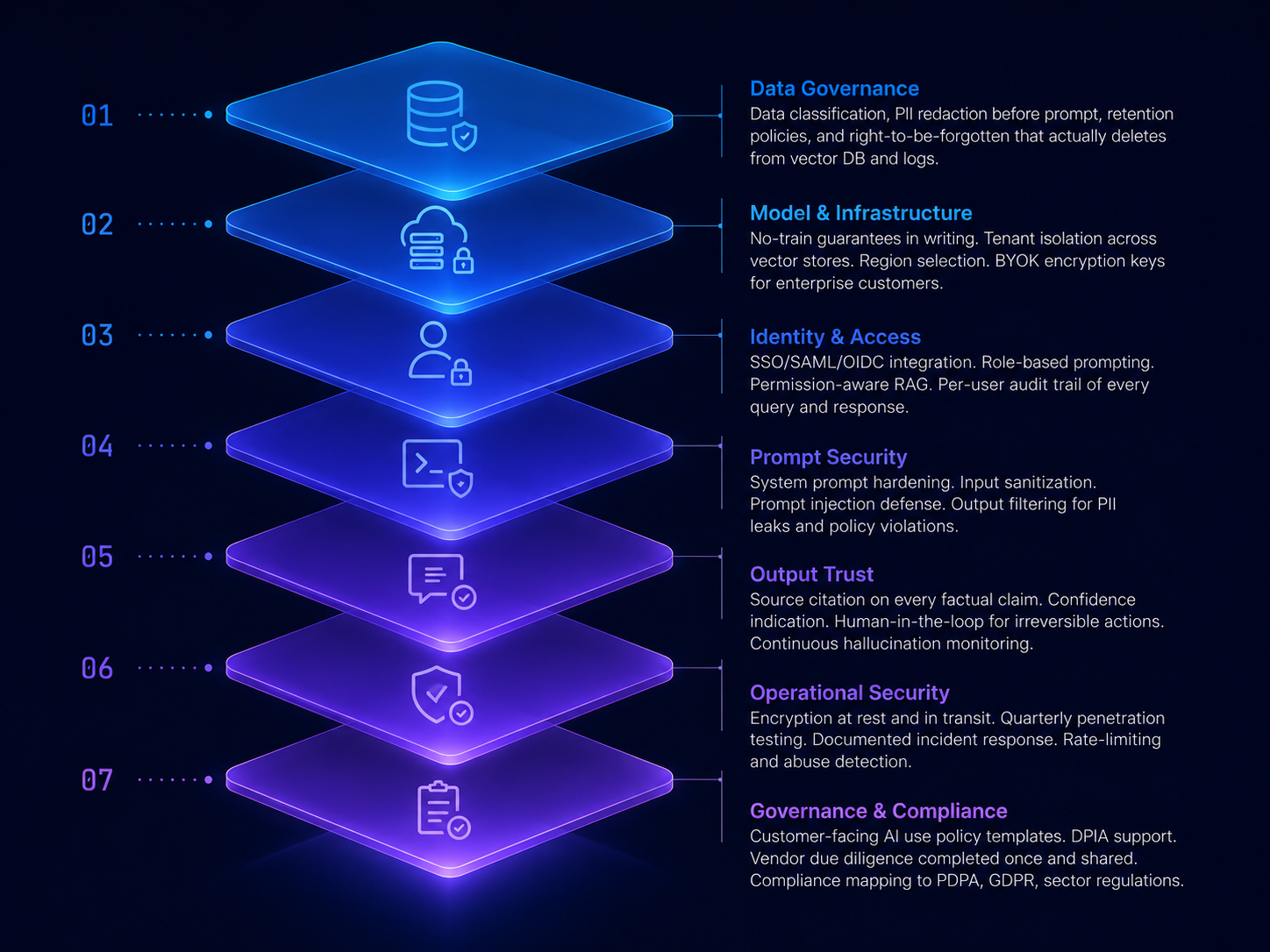
Data classification, PII redaction before prompt, retention policies, and right-to-be-forgotten that actually deletes from vector DB and logs.
No-train guarantees in writing. Tenant isolation across vector stores. Region selection. BYOK encryption keys for enterprise customers.
SSO/SAML/OIDC integration. Role-based prompting. Permission-aware RAG. Per-user audit trail of every query and response.
System prompt hardening. Input sanitization. Prompt injection defense. Output filtering for PII leaks and policy violations.
Source citation on every factual claim. Confidence indication. Human-in-the-loop for irreversible actions. Continuous hallucination monitoring.
Encryption at rest and in transit. Quarterly penetration testing. Documented incident response. Rate-limiting and abuse detection.
Customer-facing AI use policy templates. DPIA support. Vendor due diligence completed once and shared. Compliance mapping to PDPA, GDPR, sector regulations.
Most AI vendors retrieve every document and tell the model "please don't mention what the user can't see." That's not security — it's an instruction the model can be talked out of. We do it differently.
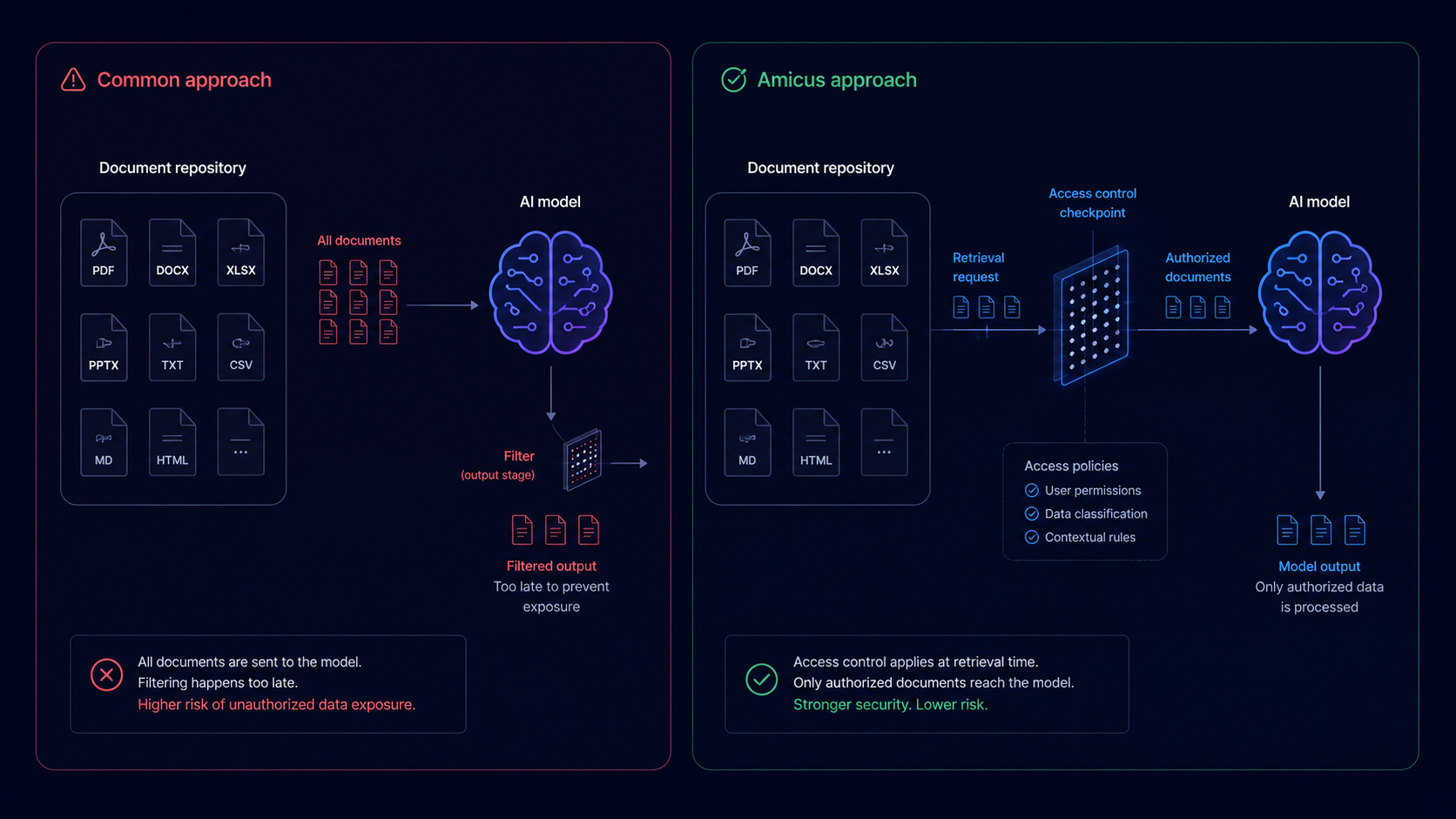
The model "sees" documents the user shouldn't. A clever prompt — or just a confused model — can leak them. Compliance theatre.
The user's identity and role determine what enters the AI's context. The model literally cannot leak what it never received.
For Thai businesses, cross-border data flow isn't a footnote — it's PDPA compliance. We make region a first-class decision, not a hidden default in someone else's terms of service.
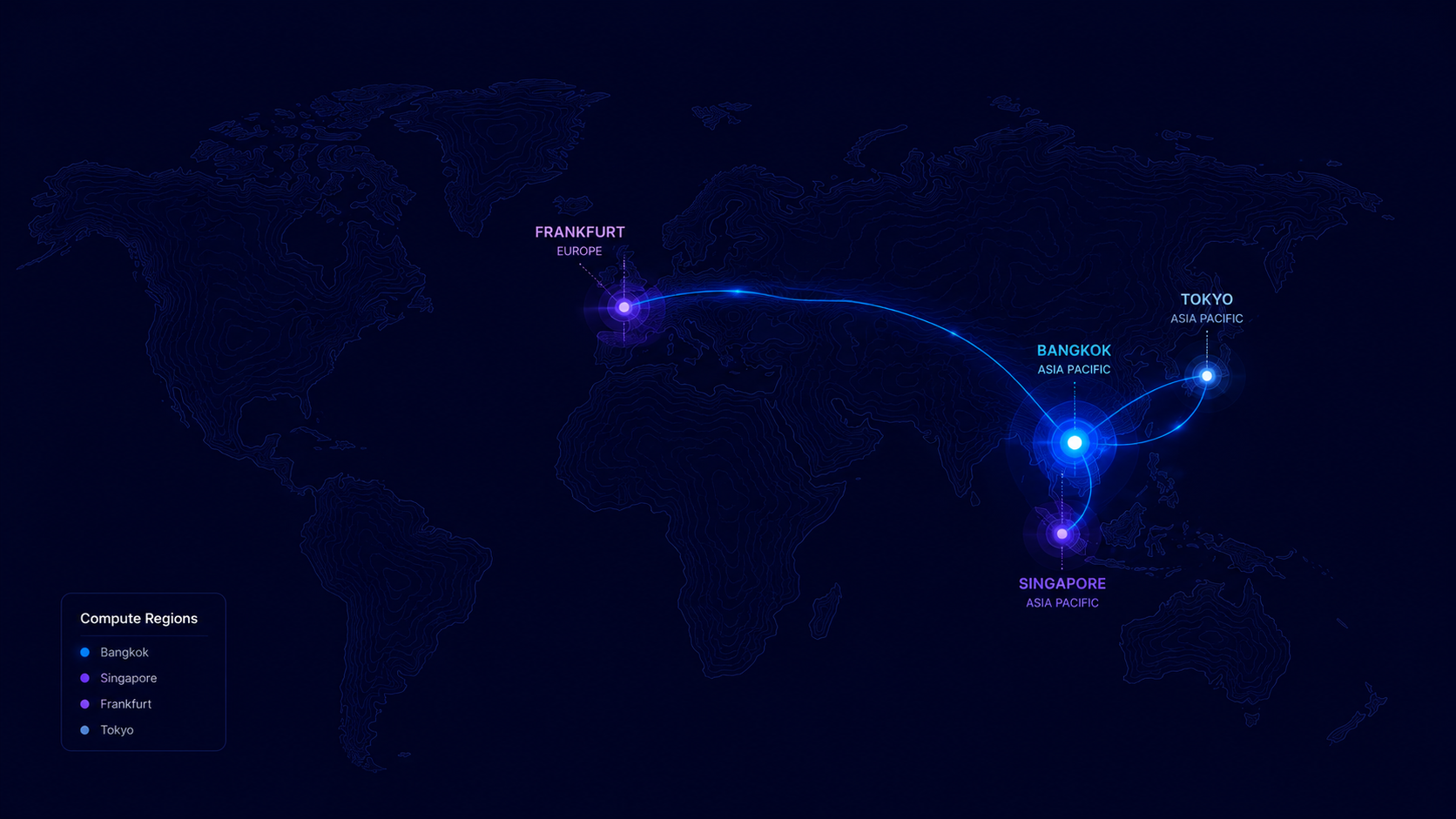
AWS / GCP / Azure regions in Singapore. Sub-millisecond latency to Bangkok. Default for most Thai SME deployments.
For regulated industries (FSI, healthcare, government). Compute and storage stay onshore. Available on enterprise tier.
Deploy into your own cloud account. We bring the software; your team owns the data plane. For maximum sovereignty.
Not every product needs the same security posture. We map our products to your data classification — so you don't over-engineer a marketing chatbot or under-engineer a contracts assistant.
| Data classification | Public | Internal | Confidential | Restricted |
|---|---|---|---|---|
| Chat Agent (CX) | ✓ Default | ✓ Standard | ✓ Enterprise tier | ✓ With BYOK + audit |
| Analytics | ✓ Default | ✓ Standard | ✓ Enterprise tier | ✓ With BYOK + audit |
| Communication Agent | ✓ Default | ✓ Standard | ✓ Enterprise tier | ✓ Customer VPC required |
| Lens.AI (HR) | — | ✓ Standard | ✓ Enterprise tier | ✓ Customer VPC required |
| Brainstorming | ✓ Default | ✓ Standard | ✓ Enterprise tier | ✓ Customer VPC required |
| Social Research | ✓ Default | ✓ Standard | — | — |
Procurement, legal, and security teams shouldn't have to wait for a sales call. Download what you need to evaluate Amicus on your own time. We'd rather earn your trust through documents than claim it through certifications we haven't earned yet.
PDPA-aligned, drafted in English with Thai translation. Signature-ready. The version your legal team will actually let you sign.
Read DPA →Every vendor we use to deliver Amicus services — model providers, infrastructure, observability — with the data each one touches, the region they operate in, and when each one is invoked.
View live list →A starting-point AI usage policy you can adapt for your organization. Our gift to customers — adoption helper, not a sales gate.
Read template →One-page summary of how we handle data, the seven-layer architecture, and our compliance posture. For your procurement team's first read.
View one-pager →How Amicus aligns with Personal Data Protection Act B.E. 2562 — written in Thai, for Thai legal and compliance teams.
Read summary →Pre-prepared answers to common vendor security questionnaires (CAIQ-Lite, SIG-Lite, custom). Save your team a week of back-and-forth.
Request packet →